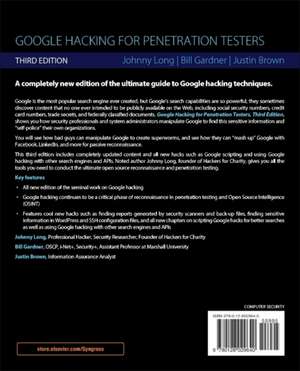
Google Hacking for Penetration Testers
Autor Bill Gardner, Johnny Long, Justin Brownen Limba Engleză Paperback – 30 noi 2015
You will learn how Google Maps and Google Earth provide pinpoint military accuracy, see how bad guys can manipulate Google to create super worms, and see how they can "mash up" Google with Facebook, LinkedIn, and more for passive reconnaissance.
This third edition includes completely updated content throughout and all new hacks such as Google scripting and using Google hacking with other search engines and APIs. Noted author Johnny Long, founder of Hackers for Charity, gives you all the tools you need to conduct the ultimate open source reconnaissance and penetration testing.
- Third edition of the seminal work on Google hacking
- Google hacking continues to be a critical phase of reconnaissance in penetration testing and Open Source Intelligence (OSINT)
- Features cool new hacks such as finding reports generated by security scanners and back-up files, finding sensitive info in WordPress and SSH configuration, and all new chapters on scripting Google hacks for better searches as well as using Google hacking with other search engines and APIs
Preț: 263.51 lei
Preț vechi: 387.81 lei
-32% Nou
Puncte Express: 395
Preț estimativ în valută:
50.42€ • 52.65$ • 41.64£
50.42€ • 52.65$ • 41.64£
Carte tipărită la comandă
Livrare economică 08-22 aprilie
Livrare express 11-15 martie pentru 79.22 lei
Preluare comenzi: 021 569.72.76
Specificații
ISBN-13: 9780128029640
ISBN-10: 0128029641
Pagini: 234
Dimensiuni: 191 x 235 x 13 mm
Greutate: 0.49 kg
Ediția:Revised
Editura: ELSEVIER SCIENCE
ISBN-10: 0128029641
Pagini: 234
Dimensiuni: 191 x 235 x 13 mm
Greutate: 0.49 kg
Ediția:Revised
Editura: ELSEVIER SCIENCE
Cuprins
Chapter 1 Google Searching Basics
Chapter 2 Advanced Operators
Chapter 3 Google Hacking Basics – The new location of the GHDB
Chapter 4 Document Grinding and Database Digging – Finding Reports Generated By Security Scanners and Back-Up Files
Chapter 5 Google’s Part in an Information Collection Framework
Chapter 6 Locating Exploits and Finding Targets
Chapter 7 Ten Simple Security Searches That Work
Chapter 8 Tracking Down Web Servers, Login Portals, and Network Hardware - Finding Sensitive WordPress and SSH Configuration
Chapter 9 Usernames, Passwords, and Secret Stuff, Oh My! – Finding GitHub, SQL, Gmail, Facebook, and other Passwords
Chapter 10 Hacking Google Services
Chapter 11 Google Hacking Showcase
Chapter 12 Protecting Yourself from Google Hackers
Chapter 13 Scripting Google Hacking For Better Searching
Chapter 14 Using Google Hacking with Other Web Search Engines and APIs
Chapter 2 Advanced Operators
Chapter 3 Google Hacking Basics – The new location of the GHDB
Chapter 4 Document Grinding and Database Digging – Finding Reports Generated By Security Scanners and Back-Up Files
Chapter 5 Google’s Part in an Information Collection Framework
Chapter 6 Locating Exploits and Finding Targets
Chapter 7 Ten Simple Security Searches That Work
Chapter 8 Tracking Down Web Servers, Login Portals, and Network Hardware - Finding Sensitive WordPress and SSH Configuration
Chapter 9 Usernames, Passwords, and Secret Stuff, Oh My! – Finding GitHub, SQL, Gmail, Facebook, and other Passwords
Chapter 10 Hacking Google Services
Chapter 11 Google Hacking Showcase
Chapter 12 Protecting Yourself from Google Hackers
Chapter 13 Scripting Google Hacking For Better Searching
Chapter 14 Using Google Hacking with Other Web Search Engines and APIs
Recenzii
"This book should be a required read for system administrators and infosec pros in general, as it gives a sobering overview of what type of information that should not be publicly available can be found online - if you know how to look for it." --Help Net Security