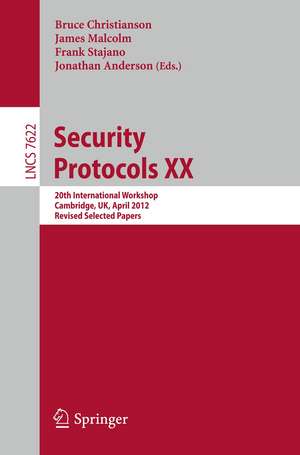
Security Protocols XX: 20th International Workshop, Cambridge, UK, April 12-13, 2012, Revised Selected Papers: Lecture Notes in Computer Science, cartea 7622
Editat de Bruce Christianson, James Malcolm, Frank Stajano, Jonathan Andersonen Limba Engleză Paperback – 21 noi 2012
Din seria Lecture Notes in Computer Science
- 20%
 Preț: 1040.03 lei
Preț: 1040.03 lei - 20%
 Preț: 333.46 lei
Preț: 333.46 lei - 20%
 Preț: 335.08 lei
Preț: 335.08 lei - 20%
 Preț: 444.17 lei
Preț: 444.17 lei - 20%
 Preț: 238.01 lei
Preț: 238.01 lei - 20%
 Preț: 333.46 lei
Preț: 333.46 lei - 20%
 Preț: 438.69 lei
Preț: 438.69 lei -
 Preț: 440.52 lei
Preț: 440.52 lei - 20%
 Preț: 336.71 lei
Preț: 336.71 lei - 20%
 Preț: 148.66 lei
Preț: 148.66 lei - 20%
 Preț: 310.26 lei
Preț: 310.26 lei - 20%
 Preț: 256.27 lei
Preț: 256.27 lei - 20%
 Preț: 632.22 lei
Preț: 632.22 lei - 17%
 Preț: 427.22 lei
Preț: 427.22 lei - 20%
 Preț: 641.78 lei
Preț: 641.78 lei - 20%
 Preț: 307.71 lei
Preț: 307.71 lei - 20%
 Preț: 1053.45 lei
Preț: 1053.45 lei - 20%
 Preț: 579.56 lei
Preț: 579.56 lei -
 Preț: 373.56 lei
Preț: 373.56 lei - 20%
 Preț: 330.23 lei
Preț: 330.23 lei - 15%
 Preț: 429.74 lei
Preț: 429.74 lei - 20%
 Preț: 607.39 lei
Preț: 607.39 lei - 20%
 Preț: 538.29 lei
Preț: 538.29 lei -
 Preț: 389.48 lei
Preț: 389.48 lei - 20%
 Preț: 326.98 lei
Preț: 326.98 lei - 20%
 Preț: 1386.07 lei
Preț: 1386.07 lei - 20%
 Preț: 1003.66 lei
Preț: 1003.66 lei - 20%
 Preț: 567.60 lei
Preț: 567.60 lei - 20%
 Preț: 575.48 lei
Preț: 575.48 lei - 20%
 Preț: 571.63 lei
Preț: 571.63 lei - 20%
 Preț: 747.79 lei
Preț: 747.79 lei - 15%
 Preț: 568.74 lei
Preț: 568.74 lei - 17%
 Preț: 360.19 lei
Preț: 360.19 lei - 20%
 Preț: 504.57 lei
Preț: 504.57 lei - 20%
 Preț: 172.69 lei
Preț: 172.69 lei - 20%
 Preț: 369.12 lei
Preț: 369.12 lei - 20%
 Preț: 346.40 lei
Preț: 346.40 lei - 20%
 Preț: 574.05 lei
Preț: 574.05 lei -
 Preț: 402.62 lei
Preț: 402.62 lei - 20%
 Preț: 584.40 lei
Preț: 584.40 lei - 20%
 Preț: 747.79 lei
Preț: 747.79 lei - 20%
 Preț: 809.19 lei
Preț: 809.19 lei - 20%
 Preț: 649.49 lei
Preț: 649.49 lei - 20%
 Preț: 343.16 lei
Preț: 343.16 lei - 20%
 Preț: 309.90 lei
Preț: 309.90 lei - 20%
 Preț: 122.89 lei
Preț: 122.89 lei
Preț: 297.51 lei
Preț vechi: 371.88 lei
-20% Nou
Puncte Express: 446
Preț estimativ în valută:
56.94€ • 59.14$ • 47.29£
56.94€ • 59.14$ • 47.29£
Carte tipărită la comandă
Livrare economică 03-17 februarie 25
Preluare comenzi: 021 569.72.76
Specificații
ISBN-13: 9783642356933
ISBN-10: 3642356931
Pagini: 288
Ilustrații: X, 277 p. 29 illus.
Dimensiuni: 155 x 235 x 15 mm
Greutate: 0.41 kg
Ediția:2012
Editura: Springer Berlin, Heidelberg
Colecția Springer
Seriile Lecture Notes in Computer Science, Security and Cryptology
Locul publicării:Berlin, Heidelberg, Germany
ISBN-10: 3642356931
Pagini: 288
Ilustrații: X, 277 p. 29 illus.
Dimensiuni: 155 x 235 x 15 mm
Greutate: 0.41 kg
Ediția:2012
Editura: Springer Berlin, Heidelberg
Colecția Springer
Seriile Lecture Notes in Computer Science, Security and Cryptology
Locul publicării:Berlin, Heidelberg, Germany
Public țintă
ResearchCuprins
Introduction: Bringing Protocols to Life (Transcript of Discussion).- Secure Internet Voting Protocol for Overseas Military Voters.- Secure Internet Voting Protocol for Overseas Military Voters
(Transcript of Discussion).- Self-enforcing Electronic Voting.- Self-enforcing Electronic Voting (Transcript of Discussion).- Approaches to Modelling Security Scenarios with Domain-Specific
Languages.- Approaches to Modelling Security Scenarios with Domain-Specific
Languages (Transcript of Discussion).- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail.- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail (Transcript of Discussion).- Statistical Metrics for Individual Password Strength.- Statistical Metrics for Individual Password Strength
(Transcript of Discussion).- Street-Level Trust Semantics for Attribute Authentication.- Street-Level Trust Semantics for Attribute Authentication
(Transcript of Discussion).- Analysis of Issues and Challenges of E-Voting in the UK.- Analysis of Issues and Challenges of E-Voting in the UK
(Transcript of Discussion).- Protocol Governance: The Elite, or the Mob?.- Protocol Governance: The Elite, or the Mob?
(Transcript of Discussion).- Usability Issues in Security.- Usability Issues in Security (Transcript of Discussion).- Usable Privacy by Visual and Interactive Control of Information
Flow.- Usable Privacy by Visual and Interactive Control of Information
Flow (Transcript of Discussion).- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System.- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System (Transcript of Discussion).- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices.- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices
(Transcript of Discussion).- Stayin’ Alive: Aliveness as an Alternative to Authentication.- Stayin’ Alive: Aliveness as an Alternative to Authentication
(Transcript of Discussion).- Paul Revere Protocols.- Paul Revere Protocols (Transcript of Discussion).- The Last Word.
Secure Internet Voting Protocol for Overseas Military Voters.- Secure Internet Voting Protocol for Overseas Military Voters
(Transcript of Discussion).- Self-enforcing Electronic Voting.- Self-enforcing Electronic Voting (Transcript of Discussion).- Approaches to Modelling Security Scenarios with Domain-Specific
Languages.- Approaches to Modelling Security Scenarios with Domain-Specific
Languages (Transcript of Discussion).- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail.- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail (Transcript of Discussion).- Statistical Metrics for Individual Password Strength.- Statistical Metrics for Individual Password Strength(Transcript of Discussion).- Street-Level Trust Semantics for Attribute Authentication.- Street-Level Trust Semantics for Attribute Authentication
(Transcript of Discussion).- Analysis of Issues and Challenges of E-Voting in the UK.- Analysis of Issues and Challenges of E-Voting in the UK
(Transcript ofDiscussion).- Protocol Governance: The Elite, or the Mob?.- Protocol Governance: The Elite, or the Mob?
(Transcript of Discussion).- Usability Issues in Security.- Usability Issues in Security (Transcript of Discussion).- Usable Privacy by Visual and Interactive Control of Information
Flow.- Usable Privacy by Visual and Interactive Control of Information
Flow (Transcript of Discussion).- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System.- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System (Transcript of Discussion).- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices.- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices
(Transcript of Discussion).- Stayin’ Alive: Aliveness as an Alternative to Authentication.- Stayin’ Alive: Aliveness as an Alternative to Authentication
(Transcript of Discussion).- Paul Revere Protocols.- Paul Revere Protocols (Transcript of Discussion).- The Last Word
(Transcript of Discussion).- Self-enforcing Electronic Voting.- Self-enforcing Electronic Voting (Transcript of Discussion).- Approaches to Modelling Security Scenarios with Domain-Specific
Languages.- Approaches to Modelling Security Scenarios with Domain-Specific
Languages (Transcript of Discussion).- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail.- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail (Transcript of Discussion).- Statistical Metrics for Individual Password Strength.- Statistical Metrics for Individual Password Strength
(Transcript of Discussion).- Street-Level Trust Semantics for Attribute Authentication.- Street-Level Trust Semantics for Attribute Authentication
(Transcript of Discussion).- Analysis of Issues and Challenges of E-Voting in the UK.- Analysis of Issues and Challenges of E-Voting in the UK
(Transcript of Discussion).- Protocol Governance: The Elite, or the Mob?.- Protocol Governance: The Elite, or the Mob?
(Transcript of Discussion).- Usability Issues in Security.- Usability Issues in Security (Transcript of Discussion).- Usable Privacy by Visual and Interactive Control of Information
Flow.- Usable Privacy by Visual and Interactive Control of Information
Flow (Transcript of Discussion).- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System.- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System (Transcript of Discussion).- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices.- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices
(Transcript of Discussion).- Stayin’ Alive: Aliveness as an Alternative to Authentication.- Stayin’ Alive: Aliveness as an Alternative to Authentication
(Transcript of Discussion).- Paul Revere Protocols.- Paul Revere Protocols (Transcript of Discussion).- The Last Word.
Secure Internet Voting Protocol for Overseas Military Voters.- Secure Internet Voting Protocol for Overseas Military Voters
(Transcript of Discussion).- Self-enforcing Electronic Voting.- Self-enforcing Electronic Voting (Transcript of Discussion).- Approaches to Modelling Security Scenarios with Domain-Specific
Languages.- Approaches to Modelling Security Scenarios with Domain-Specific
Languages (Transcript of Discussion).- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail.- The Casino and the OODA Loop: Why Our Protocols Always
Eventually Fail (Transcript of Discussion).- Statistical Metrics for Individual Password Strength.- Statistical Metrics for Individual Password Strength(Transcript of Discussion).- Street-Level Trust Semantics for Attribute Authentication.- Street-Level Trust Semantics for Attribute Authentication
(Transcript of Discussion).- Analysis of Issues and Challenges of E-Voting in the UK.- Analysis of Issues and Challenges of E-Voting in the UK
(Transcript ofDiscussion).- Protocol Governance: The Elite, or the Mob?.- Protocol Governance: The Elite, or the Mob?
(Transcript of Discussion).- Usability Issues in Security.- Usability Issues in Security (Transcript of Discussion).- Usable Privacy by Visual and Interactive Control of Information
Flow.- Usable Privacy by Visual and Interactive Control of Information
Flow (Transcript of Discussion).- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System.- Sense-And-Trace: A Privacy Preserving Distributed Geolocation
Tracking System (Transcript of Discussion).- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices.- Am I in Good Company? A Privacy-Protecting Protocol
for Cooperating Ubiquitous Computing Devices
(Transcript of Discussion).- Stayin’ Alive: Aliveness as an Alternative to Authentication.- Stayin’ Alive: Aliveness as an Alternative to Authentication
(Transcript of Discussion).- Paul Revere Protocols.- Paul Revere Protocols (Transcript of Discussion).- The Last Word
Textul de pe ultima copertă
This book constitutes the thoroughly refereed post-workshop proceedings of the 20th International Workshop on Security Protocols, held in Cambridge, UK, in April 2012.
Following the tradition of this workshop series, each paper war revised by the authors to incorporate ideas from the workshop, and is followed in these proceedings by an edited transcription of the presentation and ensuing discussion. The volume contains 14 papers with their transcriptions as well as an introduction, i.e. 29 contributions in total. The theme of the workshop was "Bringing protocols to life".
Following the tradition of this workshop series, each paper war revised by the authors to incorporate ideas from the workshop, and is followed in these proceedings by an edited transcription of the presentation and ensuing discussion. The volume contains 14 papers with their transcriptions as well as an introduction, i.e. 29 contributions in total. The theme of the workshop was "Bringing protocols to life".
Caracteristici
Up-to-date results Fast-track conference proceedings State-of-the-art research